MacOS Version Affected: 10.14.6 (Mojave) and 10.15.x (Catalina)
Safari Version Affected: 13.0.x and newer
Description:
Client-side certificates used for validating users through IIS may not work with the latest versions of MacOS and Safari. This means that any web browser login requiring the user to present a certificate as part of their authentication may potentially have issues.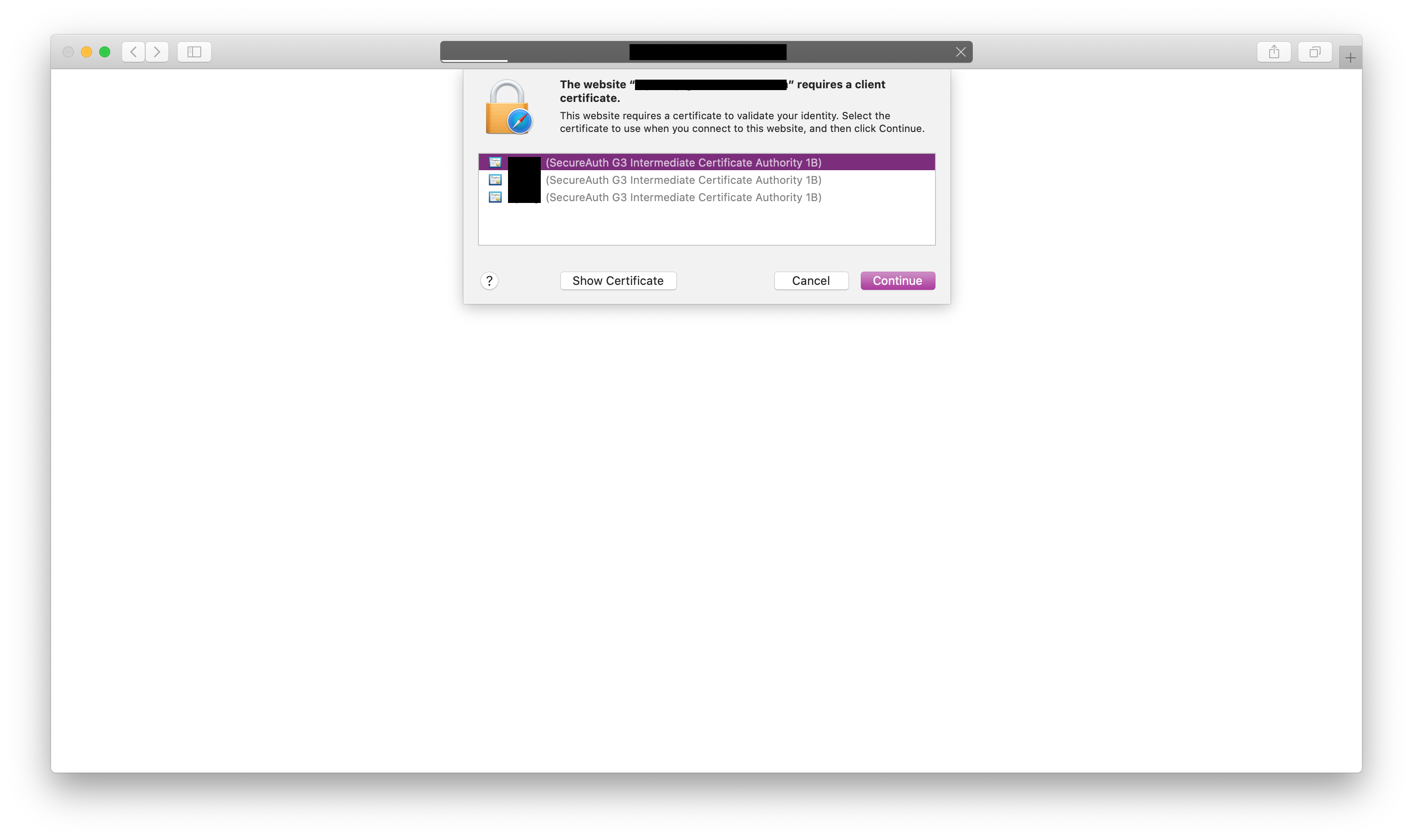
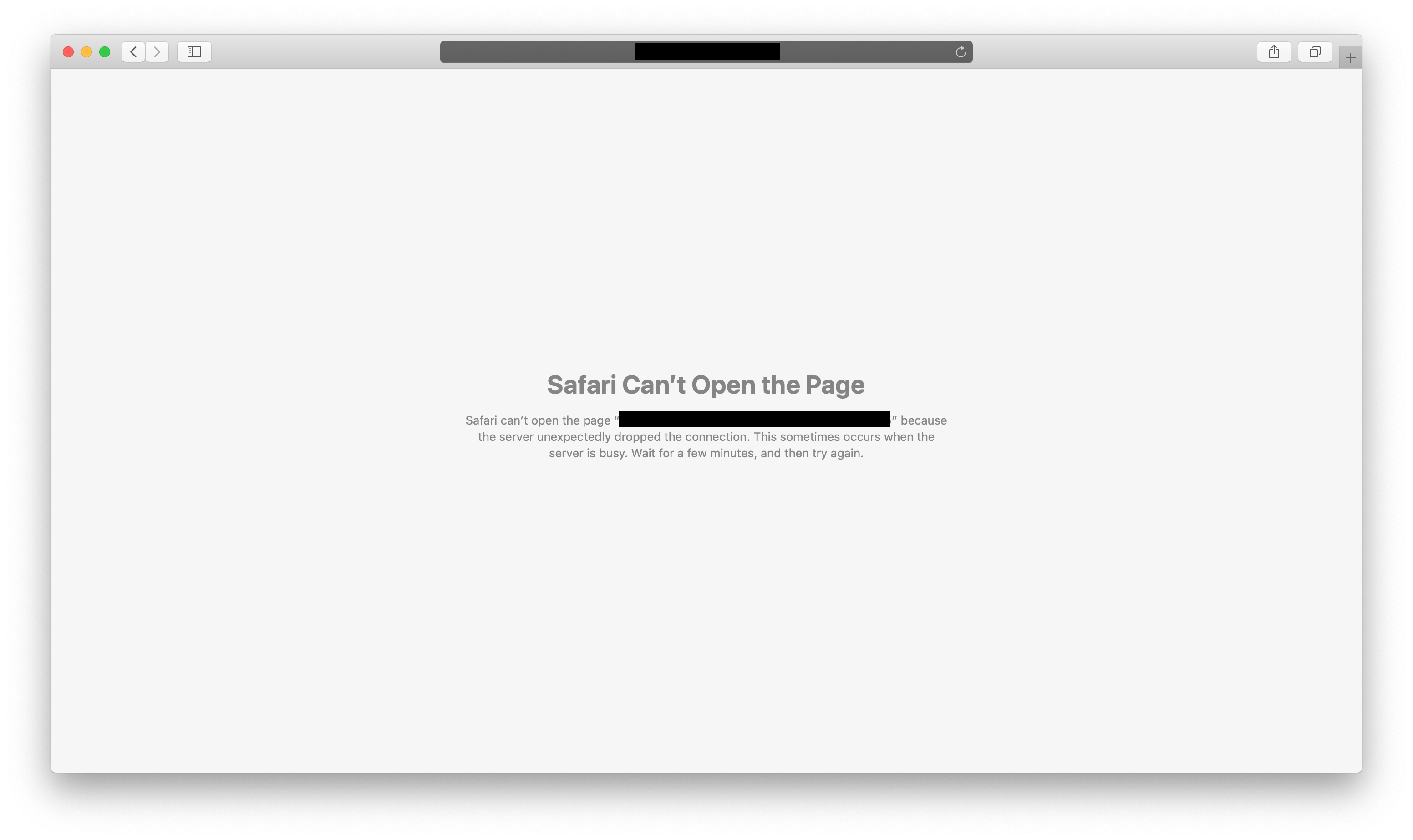
Error message may include "the server unexpectedly dropped the connection" or "the operation couldn't be completed" or "Error 9816" when choosing a valid certificate.
Some examples of workflows that may be affected by this issue would be Citrix Receiver-AGEE Client Certificate Authentication and SecureAuth's Certificate Authentication via SSL (C-SSL). Cisco Anyconnect VPN Clients may be affected, but it does look like the newer versions of MacOS v10.15 and Cisco Anyconnect VPN Client v4.8 work.
Cause:
Apple support has responded by saying that it is perhaps likely a bug and is continuing to investigate. There is little transparency on what the investigation is like and information regarding whether it will likely be fixed has not been released.
Resolution:
We have been told to use third-party web browsers for the meantime as they seem to be working with the Client Certificate Authentication according to our tests. The following have been tested and seem to work on MacOS for the meantime.
Chrome
Firefox
Apple support has mentioned that this could perhaps be fixed in later versions. With each update, there is a possibility that client certificate authentication could start working again on a specific MacOS or Safari version.
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.