SecureAuth IdP Version Affected: 9.2+
Description: When configuring a SAML integration, the service provider throws a signature error.
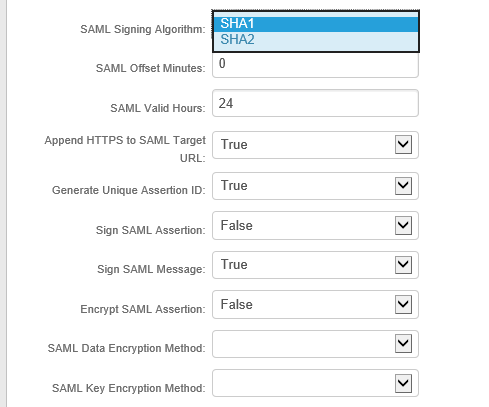
Cause: There are various reasons to why a signature error could be invoked. One of the more common ways is if it is expecting a SHA1 or SHA2 signing algorithm and there is a mismatch.
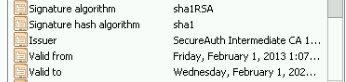
Resolution: Check if the certificate being used is SHA1 or SHA2
If a SHA1 certificate is being used, but the drop down is selected for SHA2, there will be a error.
SHA1 Certificate:
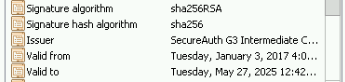
If a SHA2 certificate is being used, either dropdown can be used.
SHA2 Certificate:
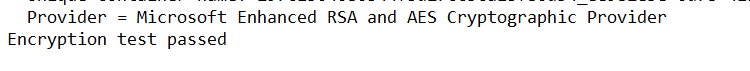
Further Troubleshooting: Open up command prompt with elevated privileges and run this command "certutil -store my > c:\temp\certinfo.txt". This will write a text file to the C:\Temp directory with information regarding the certificate on the appliance personal cert store. In order for your SHA2 certificate to be enabled for SHA2 signing, the Cryptographic Service Provider needs to be "Microsoft Enhanced RSA and AES Cryptographic Provider"
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.