SecureAuth IdP Version affected: All
Description:
When trying to log into a realm, Users are not allowed in and are informed their Password has expired, even though it hasn't.
Cause:
Inline Password Change is disabled but the settings are set to treat the password as expired after X many days and this is less than the AD Password Policy
Resolution:
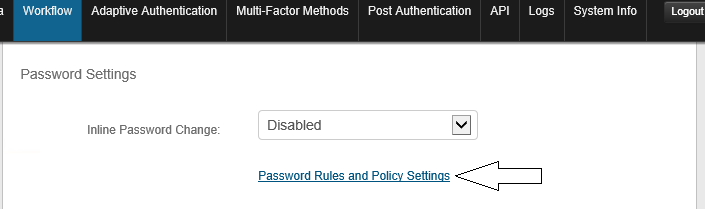
1. Open the Admin Console and Navigate to the Workflow tab of the Realm
2. Scroll down to the Password Settings section and click the link for Password Rules and Policy Settings
3. Either blank out the Password Expires Days or set it to something suitable for your environment.
In the below example, Users will not be allowed to log in after 5 days even if their AD Password is still valid.
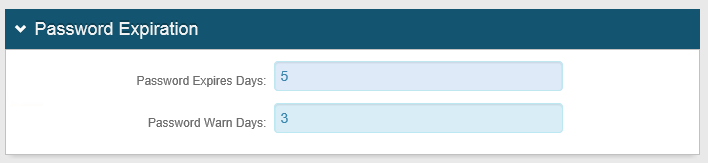
The intended purpose of this setting is to force your Users to reset their password via SecureAuth before it really expires in AD. However, if Inline Password Change is disabled, they never get the chance to change their password and so get locked out of SecureAuth.
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.