SecureAuth IdP Version affected: All
Description: This article covers allowing or preventing the use of an TOTP more than once.
Cause: Preventing the use of a TOTP more than once is the more secure option but we do leave this up to the Admin to configure.
Resolution:
To prevent the re-use of TOTP,
1. Go to the Data Tab
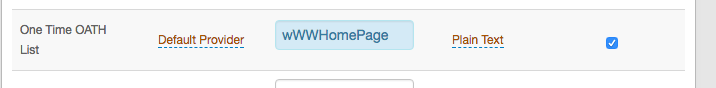
2. Scroll down to the One Time OATH list
3. Set an AD attribute in here. For example, wWWHomePage works but ensure it is not in use by another program first.
4. Mark this as Writable
5. With this setting in place on all your realms that use TOTP, the code will only be useable once.
To allow the re-use of TOTP:
As you can imagine, this is pretty much the opposite.
1. On a realm that you wish to allow the re-use of TOTP, Go to the Data Tab
2. Scroll down to the One Time OATH list
3. Remove the AD Attribute from here.
4. With this setting removed, this realm will allow the re-use of TOTP
5. On the Multifactor methods tab. You have the Password Change Interval and also the Passcode Offset length. These values combined is how long the TOTP will be valid for, minus the current clock skew.
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.