SecureAuth version affected: 9.1, 9.2
This solution has been tested on RADIUS v2.4 and v2.5
Description: Customer wants to run SA RADIUS Service under an Active Directory account.
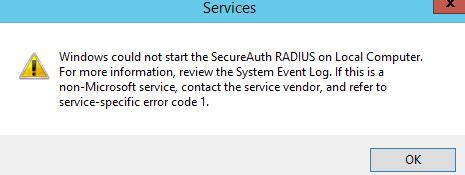
Cause: When attempting to run the RADIUS Service using an AD account, the service throws the below error.
Resolution: Create an AD account which you‘ll be using for SA RADIUS Service, the AD account should have ‘logon as a service’ permissions.
A: on IdP server, edit 'local security policy' and enable ‘logon as a service’ for that AD account.
1. Logon to the computer with administrative privileges
2. Open the ‘Administrative Tools’ and open the ‘Local Security Policy’ or you can use secpol.msc.
3. Expand ‘Local Policy’ and click on ‘User Rights Assignment’
4. In the right pane, right-click ‘Log on as a service’ and select properties.
5. Click on the ‘Add User or Group…’ button to add the new user.
6. In the ‘Select Users or Groups’ dialogue, find the user you wish to enter and click ‘OK’
7. Click ‘OK’ in the ‘Log on as a service Properties’ to save changes
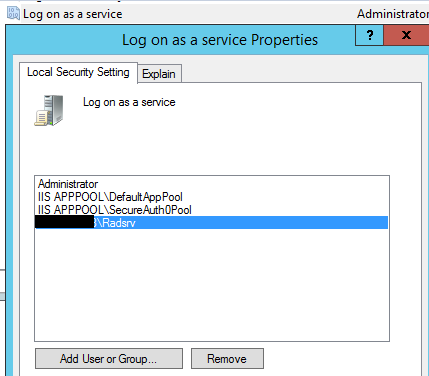
*Make sure the AD account is added here.
B: After the AD account is granted ‘logon as a service’ permissions, you’ll need to give full permissions to the AD account on the SecureAuth RADIUS installation folder:
C:\idpRADIUS or C:\Program Files (x86)\SecureAuth Corporation\SecureAuth IdP RADIUS Agent
To grant the permissions, follow these steps:
Mouse Click on the Folder | Go to Properties | Security Tab | Click ‘Edit’ Button | Click ‘Add’ Button | Search the user and Click OK | Check the box for Full Control for the AD account | Click Apply | Click OK
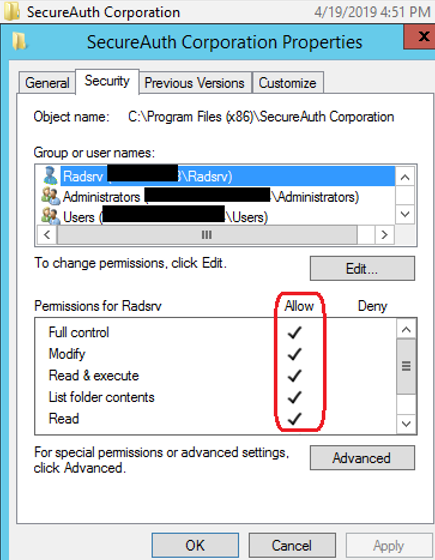
Repeat the steps to grant permission on the other Folder.
C: Change the SA RADIUS service ‘Log on as’ Local System Account to AD account, follow these steps:
- Mouse click on SA RADIUS Service | Properties | Log On Tab | Click ‘This Account’ radio button | Click ‘Browse’ | Search the AD account | Click OK | Type in the Password | Click ‘Apply’ | Click OK
- Start the RADIUS service.
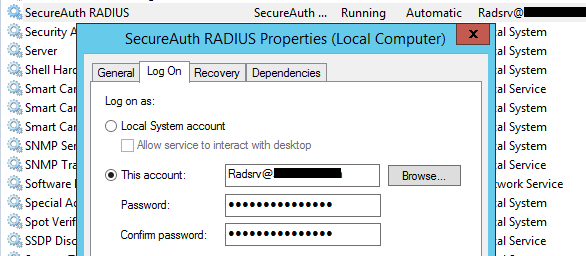
Note: When you change the SA RADIUS service ‘Log on as’ account from ‘Local System Account’ to an AD account and apply the changes, the RADIUS server settings like the ‘Shared Secret’, API Application ID and API Application Key will disappear, so we recommend to take a RADIUS configuration back up before making the changes.
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.