SecureAuth Idp Version affected: All
Description:
How to prevent specific device types from authenticating based on their User Agent string.
Cause:
For policy or technical reasons it may be necessary to block particular device types from connecting to and authenticating with IdP.
Resolution:
It's possible to block access based on specific words in user agent strings using the IIS rewrite module. To do so, follow these steps:
- Obtain the user agent string. This can be done by browsing to the following URL with the type of device to be blocked: https://www.google.co.uk/search?q=what+is+my+user+agent
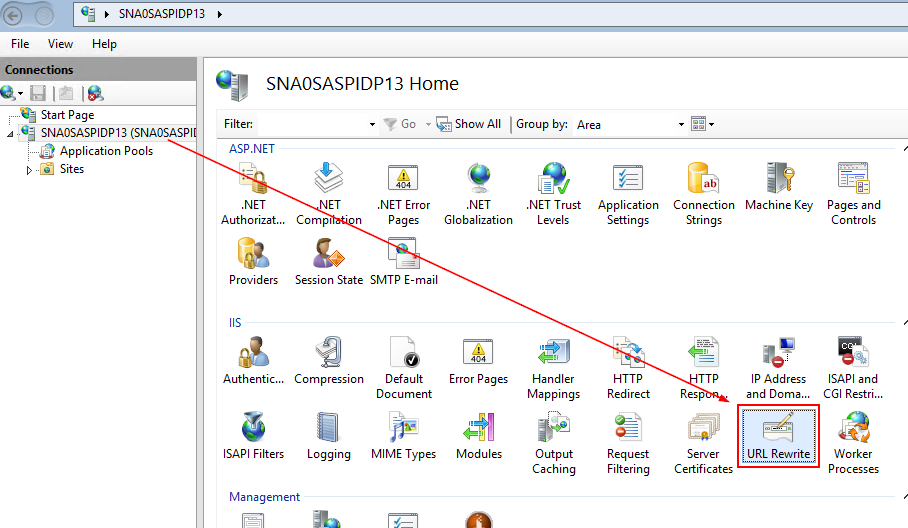
- Open IIS Manager, click on the server name then URL Rewrite
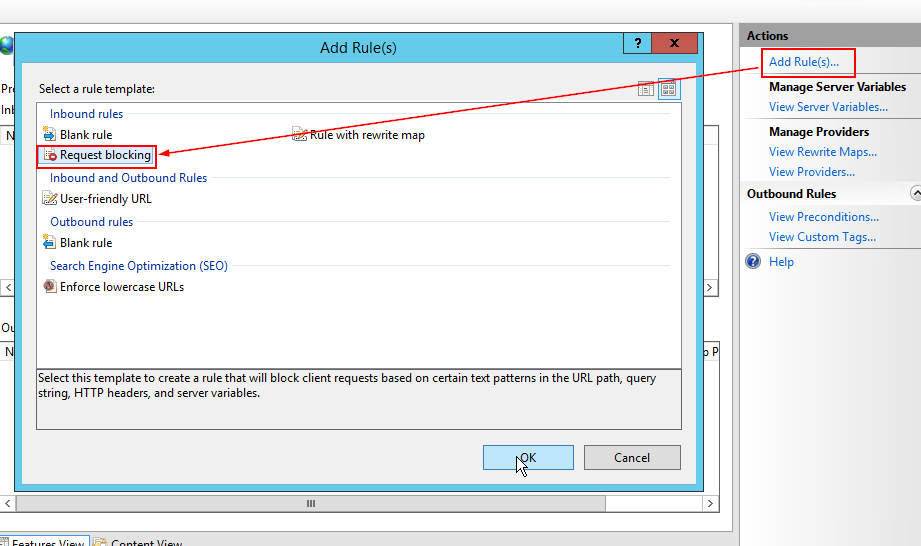
- Click Add Rule | Request Blocking
- Now choose the drop down for "Block access based on:" and select User-agent-Header.
Change the Using: drop down to Regular expressions
Then in the "Pattern" field type a list of words you want to block with a pipe | character as a separator.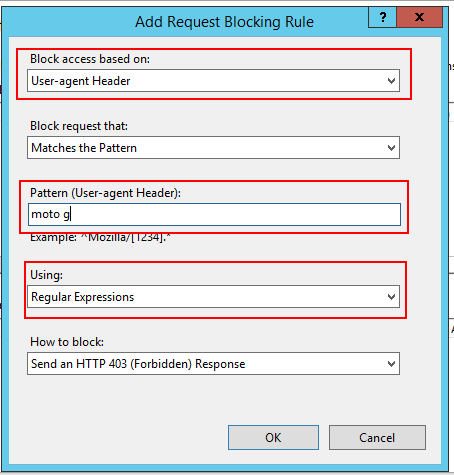
- The words you type here should be something in the user agent string specific to only the devices that should be blocked. For example this is the user agent string for a phone which is a Motorola Moto G6:
-
Mozilla/5.0 (Linux; Android 8.0.0; moto g(6) Build/OPSS27.82-87-8) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/70.0.3538.110 Mobile Safari/537.36 OPR/49.2.2361.134358
- In the example above, the model name is in the user agent string so "moto g" is used as the keyword.
- Finally there is a choice of 4 different options for "How to block:" Choose whichever method as desired.
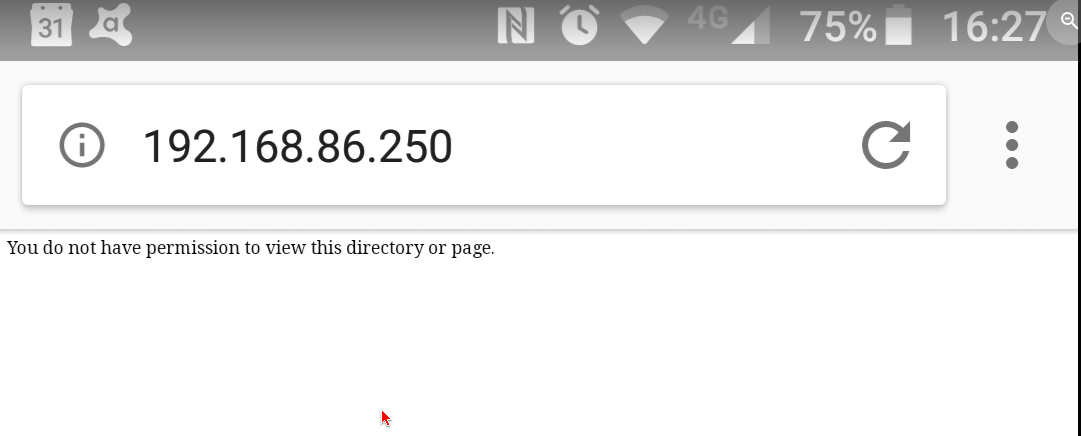
- Now when the blocked device tries to get to the IdP it will be blocked and the end user will see a message similar to the below:
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.