SecureAuth IdP Version Affected: All
Description:
When trying to delegate permissions to certain attributes in Active Directory (i.e. registeredAddress) to User Objects, you cannot find it listed in the Permissions window.
Cause:
The following list of attributes are stored within specific property sets for User Objects, which is what is actually listed as in the Permissions window:
General Information
Property set containing a set of user attributes that constitute general user information.
Applies to: User
-
Display Name
-
adminDescription
-
codePage
-
CountryCode
-
ObjectSid
-
primaryGroupID
-
sAMAccountName
-
sAMAccountType
-
sDRightsEffective
-
showInAdvancedViewOnly
-
sIDHistory
-
UID
-
comment
Personal Information
Property set containing user attributes that describe personal user information.
Applies to: Computer, Contact, User
-
streetAddress
-
homePostalAddress
-
assistant
-
info
-
country/region name
-
facsimileTelephoneNumber (fax number)
-
International-ISDN-Number
-
Locality-Name
-
MSMQ-Digests
-
mSMQSignCertificates
-
Personal-Title
-
Phone-Fax-Other
-
Phone-Home-Other
-
Phone-Home-Primary
-
otherIpPhone
-
ipPhonenumber
-
primaryInternationalISDNNumber Phone-ISDN-Primary
-
Phone-Mobile-Other (otherMobile)
-
Phone-Mobile-Primary
-
Phone-Office-Other (otherTelephone)
-
Phone-Pager-Other
-
Phone-Pager-Primary
-
physicalDeliveryOfficeName
-
thumbnailPhoto (Picture)
-
postalCode
-
preferredDeliveryMethod
-
registeredAddress
-
State-Or-Province-Name
-
Street-Address
-
telephoneNumber
-
teletexTerminalIdentifier
-
telexNumber
-
primaryTelexNumber
-
userCert
-
User-Shared-Folder
-
User-Shared-Folder-Other
-
userSMIMECertificate
-
x121Address
-
X509-Cert
Public Information
Property set containing user attributes that describe user public information.
Applies to: Computer, User
-
Additional-Information notes
-
Allowed-Attributes
-
allowedAttributesEffective
-
allowedChildClasses
-
allowedChildClassesEffective
-
altSecurityIdentities
-
Common-Name (cn)
-
company
-
department
-
description
-
displayNamePrintable
-
division
-
E-mail-Addresses
-
givenName
-
initials
-
legacyExchangeDN
-
manager
-
msDS-Approx-Immed-Subordinates
-
msDS-Auxiliary-Classes
-
distinguishedName (Obj-Dist-Name)
-
Object-Category
-
Object-Class
-
Object-Guid
-
Organization-Name
-
Organizational-Unit-Name
-
otherMailbox
-
Proxy-Addresses
-
RDN name
-
Reports (directReports)
-
servicePrincipalName
-
showInAddressBook
-
Surname
-
System-Flags
-
Text-Country/Region
-
Title
-
userPrincipalName
Private Information (2008 Domain Functional Level or newer)
Property set containing user attributes that describe user public information.
Applies to: Computer, User
-
ms-PKI-Credential-Roaming-Tokens
-
ms-PKI-RoamingTimeStamp
-
ms-PKI-DPAPIMasterKeys
-
ms-PKI-AccountCredentials
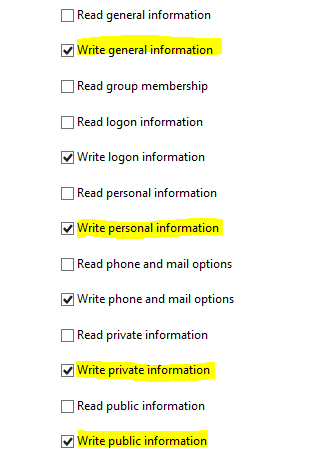
Resolution:
Find the attribute you are trying to delegate permissions to in the list above, and then delegate read/write permissions to the property set it belongs to.
Special Considerations:
From a security perspective, you will need to be aware when delegating permissions to property sets as it will allow read/write abilities to other attributes within that set, which may be more access than you want to grant to the service account in use by the IdP. If that is the case, you should review other AD attributes as potential candidates to store the user's data for IdP consumption.
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.