Applicable SecureAuth IdP Versions: All Versions
Description: The SecureAuth IdP allows 10 SAML attributes to be added to the SAML assertion by default. However, users can add additional SAML attributes to the assertion using the Extended SAML Attributes section located in the Post Authentication tab of the web admin UI.
The following steps assume that the user is using Active Directory as the data store.
Steps:
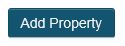
1. Go to the Profile Fields section in the Data tab of the web admin UI and click on the "Add Property" button.
2. In the new window that pops up, type in the name of the new property that you wanted mapped as the first extended SAML attribute. In this example, we are calling the new attribute "Extended Attribute 1."
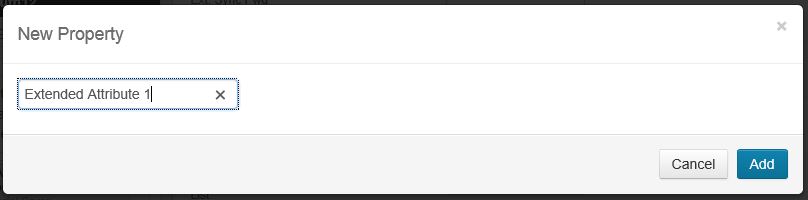
3. Click on the "Add" button to display the newly created property.
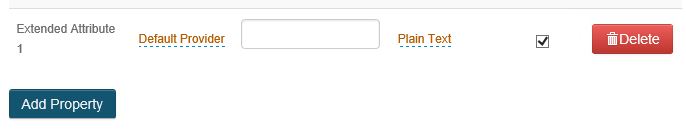
4. Type in the name of the attribute in the data store that you want this property mapped to. In this example, we are mapping it to the "extensionAttribute1" attribute of the AD data store.
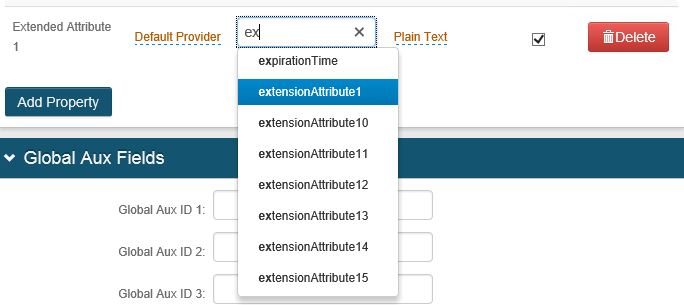
5. Once the desired attribute is chosen, click the "Save" button.

6. Go to the Post Authentication Tab configured for SAML Assertion, then click on the "Add Extended SAML Attribute" button in the "Extended SAML Attributes" section.
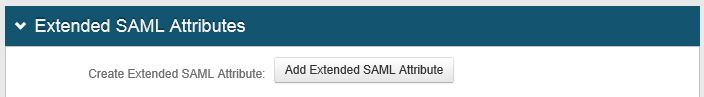
7. A message appears that a new extended attribute has been created.

8. With the extended attribute selected in the "Select Extended Attribute" drop-down menu, type in the name of the name of how you want this SAML attribute labeled in the SAML assertion, and select the appropriate property that you created via Step 3. In this example, we are labeling the attribute "ExtAttr1" and selecting the "Extended Attribute 1" value in the "Attribute Value" drop-down menu.
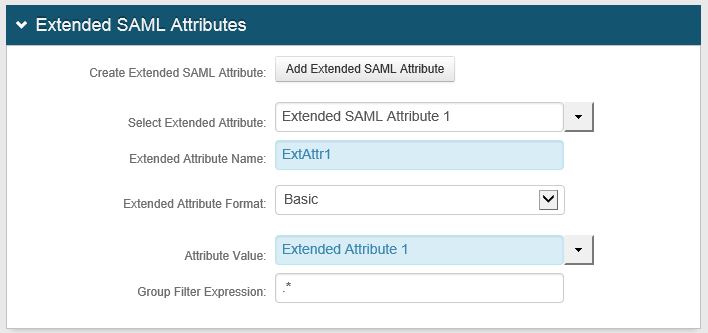
9. Click on the "Save" button to finish the creation of the extended SAML attribute.

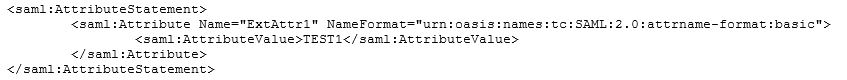
If you were to run the SAML Tracer FireFox add-on or equivalent, you should now see this extended attribute as part of the SAML assertion:
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products
Comments
Please sign in to leave a comment.