SecureAuth Idp Version affected: 7.5+
Description:
By default, the IdP does NOT validate the signature of the SSL cert from the SP in a SAML request.
Cause:
IdP version 9.1 and earlier will only validate if the realm is configured as an SP-Initiated by POST realm.
IdP version 9.2 and higher can validate signatures for SP-Initiated by POST or Redirect subject to minimum hotfix level (see below)
Resolution:
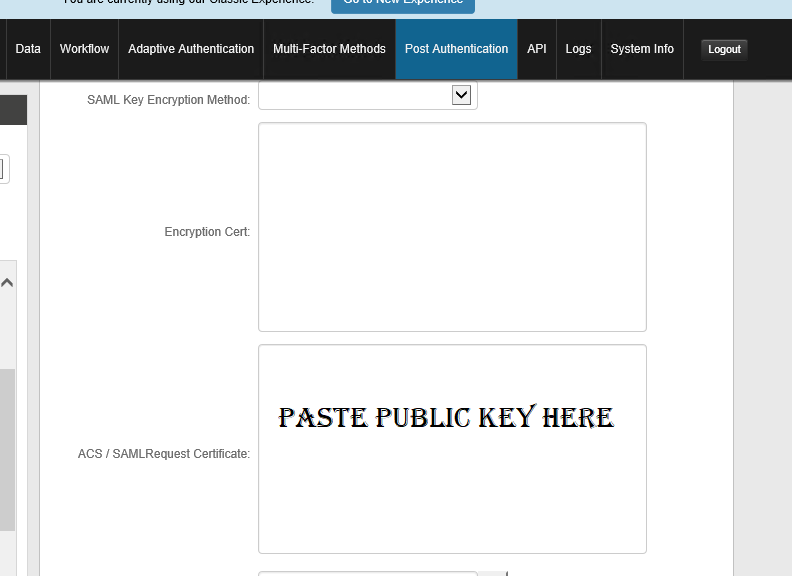
To enable signature validation for SP-Initiated configurations, copy/paste the public key of the certificate (whether publicly issued or self-signed) into the SAML Request text box under the SAML configuration.
If the certificate does not match then this error will be seen in the error log:
RequestID="a71312e9-b8eb-4656-8e15-72124861d45d" UserHostAddress="192.168.2.95" Message="SAML20SPInit exception error: Failed to receive authentication request by HTTP redirect, stack: at ComponentSpace.SAML2.Profiles.SSOBrowser.IdentityProvider.ReceiveAuthnRequestByHTTPRedirect(HttpRequest httpRequest, XmlElement& authnRequest, String& relayState, Boolean& signed, AsymmetricAlgorithm key)
at MFC.WebApp.SecureAuth.SAML20SPInit.ReceiveAuthnRequest(AuthnRequest& authnRequest, String& relayState)
Special Considerations:
The minimum required hotfix version required to support SP Init by Redirect (EE-1432):
IdP 9.3 9.3.0-16
IdP 19.07.01 19.07.01-8
SecureAuth Knowledge Base Articles provide information based on specific use cases and may not apply to all appliances or configurations. Be advised that these instructions could cause harm to the environment if not followed correctly or if they do not apply to the current use case.
Customers are responsible for their own due diligence prior to utilizing this information and agree that SecureAuth is not liable for any issues caused by misconfiguration directly or indirectly related to SecureAuth products.
Comments
Please sign in to leave a comment.